I have an odd routing issue I can’t seem to work out.
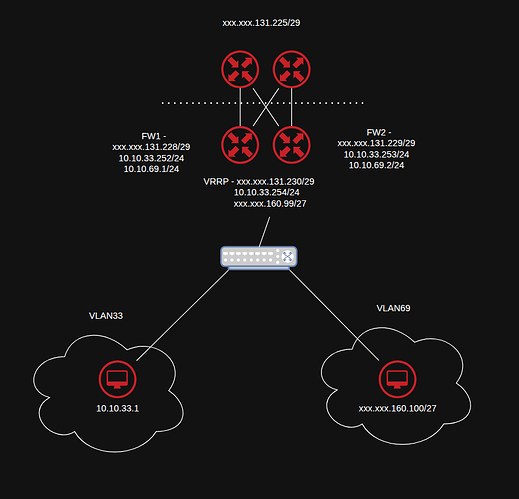
setup:
VLAN4000 - WAN xxx.xxx.131.224/29
FW1 - xxx.xxx.131.228/29
FW2 - xxx.xxx.131.229/29
VRRP - xxx.xxx.131.230/29
UPSTREAM VRRP - xxx.xxx.131.225/29
VLAN33 - INTERNAL 10.10.33.0/24 - SNAT rules for this vlan
FW1 - 10.10.33.252/24
FW2 - 10.10.33.253/24
VRRP - 10.10.33.254/24
VLAN69 - OPENSTACK xxx.xxx.160.96/27 - routed from upstream to WAN-VRRP no NAT for this vlan
FW1 - 10.10.69.1/24
FW2 - 10.10.69.2/24
VRRP xxx.xxx.160.99/27
I set this up to use the least amount of IP's in the /27.
Visual
Above the dotted line is our upstream provider.
Config Snippets
# Firewall Groups
set firewall group address-group OPENSTACK address 'xxx.xxx.160.100-xxx.xxx.160.127'
set firewall group network-group NET-VLAN33 network '10.10.33.0/24'
set firewall group network-group NET-VLAN69 network 'xxx.xxx.160.96/27'
# Firewall Forward filter
set firewall ipv4 forward filter rule 43 action 'jump'
set firewall ipv4 forward filter rule 43 inbound-interface name 'bond0.33'
set firewall ipv4 forward filter rule 43 jump-target 'VLAN33-FORWARD'
set firewall ipv4 forward filter rule 79 action 'jump'
set firewall ipv4 forward filter rule 79 inbound-interface name 'bond0.69'
set firewall ipv4 forward filter rule 79 jump-target 'VLAN69-FORWARD'
# VLAN33 Rules
set firewall ipv4 name VLAN33-FORWARD rule 3500 action 'accept'
set firewall ipv4 name VLAN33-FORWARD rule 3500 description 'Allow packets from VLAN33 to VLAN35'
set firewall ipv4 name VLAN33-FORWARD rule 3500 destination group network-group 'NET-VLAN35'
set firewall ipv4 name VLAN33-FORWARD rule 3500 source group network-group 'NET-VLAN33'
set firewall ipv4 name VLAN33-FORWARD rule 3500 state 'new'
set firewall ipv4 name VLAN33-FORWARD rule 999999 action 'drop'
set firewall ipv4 name VLAN33-FORWARD rule 999999 description 'Drop packets from VLAN33 to rfc1918 networks'
set firewall ipv4 name VLAN33-FORWARD rule 999999 destination group network-group 'NET-RFC1918'
set firewall ipv4 name VLAN33-FORWARD rule 999999 inbound-interface name 'bond0.33'
set firewall ipv4 name VLAN33-FORWARD rule 999999 state 'new'
# VLAN69 Rules
set firewall ipv4 name VLAN69-FORWARD default-action 'accept'
set firewall ipv4 name VLAN69-FORWARD description 'VLAN69 (public)'
set firewall ipv4 name VLAN69-FORWARD rule 999999 action 'drop'
set firewall ipv4 name VLAN69-FORWARD rule 999999 description 'Drop packets from VLAN69 to rfc1918 networks'
set firewall ipv4 name VLAN69-FORWARD rule 999999 destination group network-group 'NET-RFC1918'
set firewall ipv4 name VLAN69-FORWARD rule 999999 inbound-interface name 'bond0.69'
set firewall ipv4 name VLAN69-FORWARD rule 999999 state 'new'
# NAT
set nat source rule 201033 description 'VLAN33 (os-ext) via WAN Connection'
set nat source rule 201033 destination address '!xxx.xxx.160.96/27'
set nat source rule 201033 outbound-interface name 'bond0.4000'
set nat source rule 201033 source address '10.10.33.0/24'
set nat source rule 201033 translation address 'xxx.xxx.131.230'
# Static routes
set protocols static route 0.0.0.0/0 next-hop xxx.xxx.131.225 distance '201'
# Wan-load-balance
set load-balancing wan rule 13 destination address 'xxx.xxx.160.96/27'
set load-balancing wan rule 13 exclude
set load-balancing wan rule 13 inbound-interface 'any'
VLAN33 can reach internet and other local vlans apart from the puplic ip block in VLAN69, when monitoring traffic doing mtr to an IP in VLAN69 it goes out of bond0.400 not being natted or translated as far as I can see.
VLAN69 can also route out to the internet but can’t get to VLAN33 , which is expected in firewall name VLAN69-FORWARD rule 999999 to dtop RFC1918
Not sure what I am missing here, as VLAN69 is directly connected to FW1 & 2, so there should be no reason for VLAN33 not to be able to get to VLAN69.