Hi all, I’m trying to set up a connection to Mullvad using 1.4-rolling-202111200317, and the connection is up and handshaking, but I can’t send any data over it. Regardless of routing, should I still just be able to ping over that interface (ping -I wg1 1.1.1.1) and get a response?
As you can see in my configuration below, I’m trying to route a specific network group via the VPN, but the route doesn’t appear in the routing table. I’m new to zone-policy and PBR though, so I’m not sure if it’s meant to. But regardless, shouldn’t I still be able to ping or do some other kind of test to get data over that interface, regardless of routing?
The reason I have both eth1 and pppoe0 as my WAN interface in the config is that I’m prototyping it on my existing network. Occasionally I have been testing functionality direct to the internet, when I switch to the pppoe0 connection to my ISP (hardening some of the rules as I do). It’s currently disabled. I haven’t had any other problems with this config, though, whether using pppoe0 or eth1 directly as my WAN interface. I have a wireguard roadwarrior working well, as is everything else. I just haven’t been able to traffic data over my mullvad connection.
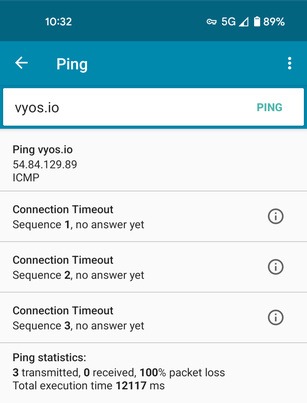
I’ve tried having the firewall off completely, and I’ve tried other VPN providers. They all handshake but I’m unable to ping via it. Don’t worry too much about the mtu and mss settings in the below, they’re just something I’ve been playing with for another reason, but I’ve removed all of those and found the same behaviour. I think there is something very basic about routing that I’ve misunderstood.
Any guidance appreciated, if there are any log outputs that will help please let me know what commands will provide them. Many thanks.
Some info:
$ sudo wg
interface: wg1
public key: xxxxxx
private key: (hidden)
listening port: 39407
peer: xxxxxx
endpoint: xx.xx.xx.xx:51820
allowed ips: 0.0.0.0/0
latest handshake: 1 minute, 13 seconds ago
transfer: 9.61 KiB received, 288.95 KiB sent
persistent keepalive: every 10 seconds
# ping -I wg1 1.1.1.1
PING 1.1.1.1 (1.1.1.1) from 10.0.40.1 wg1: 56(84) bytes of data.
^C
--- 1.1.1.1 ping statistics ---
17 packets transmitted, 0 received, 100% packet loss, time 16400ms
$ route
Kernel IP routing table
Destination Gateway Genmask Flags Metric Ref Use Iface
default 192.168.1.1 0.0.0.0 UG 20 0 0 eth1
10.0.0.0 0.0.0.0 255.255.255.0 U 0 0 0 eth2
10.0.30.0 0.0.0.0 255.255.255.0 U 0 0 0 wg2
192.168.1.0 0.0.0.0 255.255.255.0 U 0 0 0 eth1
$ ip route
default nhid 11 via 192.168.1.1 dev eth1 proto static metric 20
10.0.0.0/24 dev eth2 proto kernel scope link src 10.0.0.1
10.0.30.0/24 dev wg2 proto kernel scope link src 10.0.30.1
192.168.1.0/24 dev eth1 proto kernel scope link src 192.168.1.11
My config:
container {
name adguardhome {
allow-host-networks
image adguard/adguardhome
volume conf {
destination /opt/adguardhome/conf
source /config/mine/adguardhome/conf
}
volume work {
destination /opt/adguardhome/work
source /config/mine/adguardhome/work
}
}
name pixelserv-tls {
allow-host-networks
image imthai/pixelserv-tls
volume conf {
destination /var/cache/pixelserv
source /config/mine/pixelserv-tls
}
}
}
firewall {
all-ping enable
broadcast-ping disable
config-trap disable
group {
network-group PRIVATE {
description "private ranges"
network xxx.xxx.0.0/16
network xxx.xxx.0.0/12
network xxx.xxx.0.0/8
network xxx.xxx.0.0/8
network xxx.xxx.0.0/10
}
network-group VIAVPN {
network xxx.xxx.0.128/27
network xxx.xxx.30.0/24
}
}
ipv6-receive-redirects disable
ipv6-src-route disable
ip-src-route disable
log-martians enable
name LAN-LOCAL {
default-action accept
}
name LAN-VPN {
default-action accept
}
name LAN-WAN {
default-action accept
}
name LOCAL-LAN {
default-action accept
}
name LOCAL-VPN {
default-action accept
}
name LOCAL-WAN {
default-action accept
}
name VPN-LAN {
default-action drop
enable-default-log
rule 5 {
action accept
state {
established enable
related enable
}
}
rule 6 {
action drop
log enable
state {
invalid enable
}
}
rule 10 {
action drop
description "block private networks"
log enable
source {
group {
network-group PRIVATE
}
}
}
}
name VPN-LOCAL {
default-action accept
enable-default-log
rule 5 {
action accept
state {
established enable
related enable
}
}
rule 6 {
action drop
log enable
state {
invalid enable
}
}
rule 10 {
action drop
description "block private networks"
log enable
source {
group {
network-group PRIVATE
}
}
}
rule 20 {
action accept
log enable
protocol icmp
state {
new enable
}
}
}
name WAN-LAN {
default-action drop
enable-default-log
rule 5 {
action accept
state {
established enable
related enable
}
}
rule 6 {
action drop
log enable
state {
invalid enable
}
}
rule 10 {
action drop
description "block private networks"
disable
log enable
source {
group {
network-group PRIVATE
}
}
}
}
name WAN-LOCAL {
default-action accept
enable-default-log
rule 5 {
action accept
state {
established enable
related enable
}
}
rule 6 {
action drop
log enable
state {
invalid enable
}
}
rule 10 {
action drop
description "block private networks"
disable
log enable
source {
group {
network-group PRIVATE
}
}
}
rule 20 {
action accept
description "Allow ICMP"
log enable
protocol icmp
state {
new enable
}
}
rule 30 {
action accept
description "Allow SSH"
destination {
port 22
}
log enable
protocol tcp
state {
new enable
}
}
rule 40 {
action accept
description "Allow Wireguard RoadWarrior"
destination {
port 51031
}
log enable
protocol udp
}
}
receive-redirects disable
send-redirects enable
source-validation disable
syn-cookies enable
twa-hazards-protection disable
}
interfaces {
ethernet eth1 {
address dhcp
description WAN
hw-id xx:xx:xx:xx:xx:0d
ip {
adjust-mss 1420
}
ipv6 {
address {
no-default-link-local
}
}
mtu 1492
}
ethernet eth2 {
address xxx.xxx.0.1/24
description LAN
hw-id xx:xx:xx:xx:xx:10
ip {
adjust-mss 1420
}
ipv6 {
address {
no-default-link-local
}
}
mtu 1492
policy {
route VPN
}
}
loopback lo {
}
pppoe pppoe0 {
authentication {
password xxxxxx
user xxxxxx
}
default-route auto
disable
ip {
adjust-mss 1420
}
mtu 1492
no-peer-dns
source-interface eth1
}
wireguard wg1 {
address xxx.xxx.40.1/32
description MullvadVPN
ip {
adjust-mss 1372
}
ipv6 {
address {
no-default-link-local
}
}
mtu 1412
peer au3 {
address xxx.xxx.88.2
allowed-ips xxx.xxx.0.0/0
persistent-keepalive 10
port 51820
public-key xxxxxx
}
private-key xxxxxx
}
wireguard wg2 {
address xxx.xxx.30.1/24
description RoadWarrior
ip {
adjust-mss 1372
}
ipv6 {
address {
no-default-link-local
}
}
mtu 1412
peer phone {
allowed-ips xxx.xxx.30.2/32
persistent-keepalive 15
public-key xxxxxx
}
port 51031
private-key xxxxxx
}
wireless wlan0 {
disable
hw-id xx:xx:xx:xx:xx:c4
ipv6 {
address {
no-default-link-local
}
}
physical-device phy0
}
}
nat {
source {
rule 100 {
outbound-interface pppoe0
translation {
address masquerade
}
}
rule 200 {
outbound-interface eth1
translation {
address masquerade
}
}
rule 300 {
outbound-interface wg1
translation {
address masquerade
}
}
}
}
policy {
route VPN {
rule 1 {
description "Local destinations for all traffic"
destination {
group {
network-group PRIVATE
}
}
set {
table main
}
}
rule 100 {
description "Internet destinations for viavpn clients"
destination {
address xxx.xxx.0.0/0
}
set {
table 100
}
source {
group {
network-group VIAVPN
}
}
}
}
}
protocols {
static {
table 100 {
route xxx.xxx.0.0/0 {
blackhole {
distance 255
}
interface wg1 {
}
}
}
}
}
service {
ssh {
disable-password-authentication
port 22
}
}
system {
config-management {
commit-revisions 100
}
conntrack {
modules {
ftp
h323
nfs
pptp
sip
sqlnet
tftp
}
}
console {
device ttyS0 {
speed 115200
}
}
domain-name xxxxxx
host-name xxxxxx
ipv6 {
disable
disable-forwarding
}
login {
banner {
post-login ""
pre-login ""
}
user xxxxxx {
authentication {
encrypted-password xxxxxx
public-keys [email protected] {
key xxxxxx
type ssh-rsa
}
}
home-directory /config/mine/xxxxxx
}
user xxxxxx {
authentication {
encrypted-password xxxxxx
}
}
}
name-server xxx.xxx.0.1
ntp {
server xxxxx.tld {
}
}
sysctl {
parameter net.ipv6.conf.lo.disable_ipv6 {
value 1
}
}
syslog {
global {
facility all {
level info
}
facility protocols {
level debug
}
}
}
time-zone Australia/Hobart
}
zone-policy {
zone LAN {
default-action drop
from LOCAL {
firewall {
name LOCAL-LAN
}
}
from VPN {
firewall {
name VPN-LAN
}
}
from WAN {
firewall {
name WAN-LAN
}
}
interface eth2
interface wg2
}
zone LOCAL {
default-action drop
from LAN {
firewall {
name LAN-LOCAL
}
}
from VPN {
firewall {
name VPN-LOCAL
}
}
from WAN {
firewall {
name WAN-LOCAL
}
}
local-zone
}
zone VPN {
default-action drop
from LAN {
firewall {
name LAN-VPN
}
}
from LOCAL {
firewall {
name LOCAL-VPN
}
}
interface wg1
}
zone WAN {
default-action drop
from LAN {
firewall {
name LAN-WAN
}
}
from LOCAL {
firewall {
name LOCAL-WAN
}
}
interface eth1
interface pppoe0
}
}