I have been playing with VyOS (rolling, latest snapshot) for a couple of days now. I have a decade plus experience with Linux and *BSD, and until now ran a mixture of pfSense, OPNsense and IPFire on my home edge router. I have annual subscriptions to several VPN providers, including AzireVPN and Mullvad - both of whom provide WireGuard access.
While it was a little alien at first, I very quickly started to love VyOS. It’s so elegantly simple (a bit like pf) and easy to use. A quick glance at ‘show conf’ instantly lets you spot any errors that could be causing an issue. It’s fast, too! About the only thing missing for my own use case at present, for it to completely replace OPNsense, is DNS over TLS or HTTPS (unbound, stubby, dnscrypt-proxy or similar).
I’ve deployed a VyOS instance in VMWare Workstation, with 2 virtual NICs; eth0 acts as ‘WAN’/DHCP (to my ‘real’ router) and eth1 is a VMWare Lan Segment acting as LAN interface for other VMWare client OS’. I got the actual VyOS install and basic config up and running in minutes - nice! Unfortunately I can’t get WireGuard working on it no matter what I try. Would someone please help me unpick this? I did ask on the VyOS subreddit but I’ve not had any solutions yet.
AzireVPN provides me the following config to use on my device:
“DNS”: “91.231.153.2, 2001:67c:15ec:1337::2”,
“Address”: “10.20.17.50/19, 2a07:241:1:4000::1133/64”,
“PublicKey”: “j3Yw1nWiSgz8YAGp95KrvyvUhVLCFZ5msO33KR/A0Dc=”,
“Endpoint”: “uk1.wg.azirevpn.net:51820”
As you can see, the address it wants me to use on my interface is 10.20.17.50/19. This works OK in Linux and BSD directly and using wg-quick. Unfortunately, when I try to set interface wireguard wg0 address 10.20.17.50/19 it just refuses and tells me it’s an invalid value. I did try 10.20.0.0/19 also, and while this works I can’t get any throughput that I can tell.
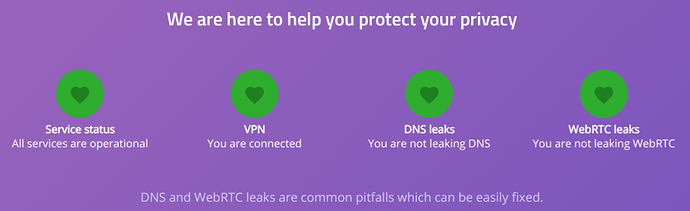
Even with the interface finally added, my VyOS install itself and all local DHCP clients still report my main ISP address (using curl ipinfo.io) rather than the wg tunnel address. Should my static route be 0.0.0.0/0 or 10.20.0.0/19 - or something else?
Also, how do I add the tunnel’s DNS? Do I use the usual ‘set service dns forwarding listen-on’ and tie it to the wg0 interface?
I did add a firewall rule in OUTSIDE-IN for UDP port 51820 (the default wg port, as used on my config) so it’s not that. Any advice would be really appreciated. The Wiki is unfortunately rather fragmented on this issue, and some of the commands are out of date. The related discussion on Github added some extra potentially usable config (as did a post on this forum) but again I’m having no luck. I can post up my full config if anyone wants to see it, but hopefully someone can spot something obviously wrong in what I posted so far and help me get off and running.
Thanks in advance!